Why internal informational systems are hacked and how to avoid this
Almost any business expands in terms of its internal systems as it grows: task trackers, file sharings, help portals, knowledge bases. The implementation of a new systems is often chaotic: it isn’t planned in advance, it isn’t budgeted and needs to be done urgently. The development of such systems isn’t always given to outsource and passed on to their own IT departments.
In most cases working according to a tight deadline, budget deficit and experienced employees results in vulnerable information systems, the drawbacks of which can be exploited by intruders.
Why internal systems aren’t that protected
Requirements for resistance to cyber attacks aren’t always clearly mentioned. Companies refuse to work on safety not only to save time and money. It is believed that internal systems don’t need protection:
"Who will hack us?"
Myth
Hacking is the intrigues of competitors and the revenge of former employees. If relations with competitors aren’t spoiled, and workers leave without conflicts, the list of people interested in hacking is reduced to hackers. And they, as it is known, "do not care about us, because we have nothing to steal." Therefore, non-targeted hacking is often considered as something distant and unlikely.
Reality
Non-targeted (random) attack is a scenario in which an intruder attacks a large number of targets, but doesn’t set himself the task of getting unauthorized access to a particular resource.
To verify that there are constant attempts to get unauthorized access, just look at the error.log of your site or similar log files of the router and firewall of any company.
With non-targeted attacks, the resource is hacked not because it belongs to any company, but because it runs on vulnerable software. Quantity is more important than quality.
Once a bug in the system component (CMS, web server, FTP, etc.) goes into the public, cybercriminals immediately begin to use it. The picture doesn’t change: only about 200 exploits are published monthly on exploit-db exploit-db, and on average about 8,000 vulnerabilities of various systems are published on cve-details.
Another common cause of hacking is the human factor: the mistakes of developers, administrators and users of the system. To take advantage of such errors, you don’t need to have high qualifications, have access to serious computation power or know the magic word. Magic query in the search engine - google hacking is enough.
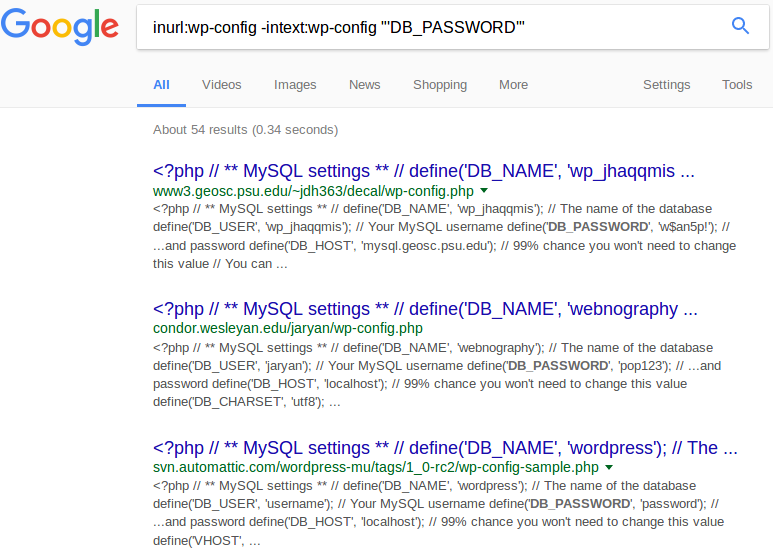
Sometimes a simple search query is enough to get a password. Once you get the employees’ accounts, getting into the company network and getting to the internal resources won’t be a big deal
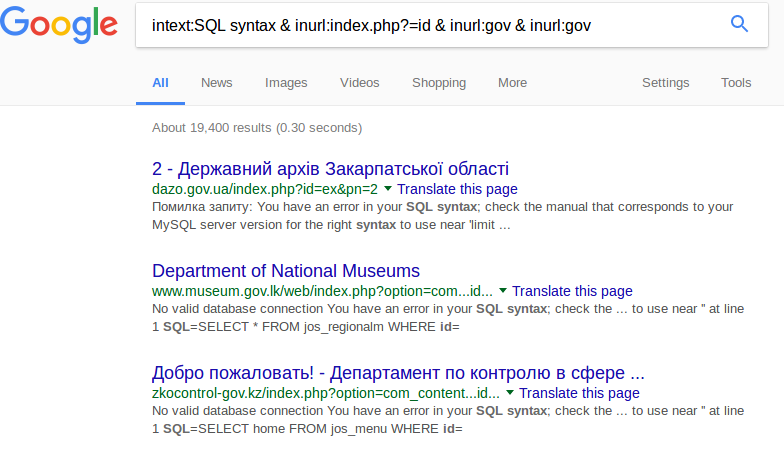
An example of a search query that shows resources that aren’t properly configured for error handling, which greatly simplifies the SQL injection attack
"Our resource is available only from the local network"
Myth
If a service is available only on a local network or VPN, it is very difficult to hack it. So you do not need any extra protection.
Reality
To connect to the local network of the vast majority of organizations is not as difficult as it seems. The entry point can be any network node accessible from the outside, for example, a router or a printer.
Think of examples of infection with viruses-extortionists "WannaCry" in May 2017. That time even large organizations were affected, the security of which wasn’t questioned: German railways, British hospitals, French industry.
Even after the cyber attack was analyzed in the media, the companies didn’t take steps to prevent similar incidents in the future. In June, a new wave of infection began with the cryptographers "Petya" and "NotPetya", which used the same vulnerability closed in March 2017 for the distribution. The infection of one computer led to the defeat of a large part of the local network and the reason of it was also that their security wasn’t so closely watched - as they aren’t connected to the Internet.
In any case, hitting local resources and exploiting their vulnerabilities is an integral part of cyberattacks.
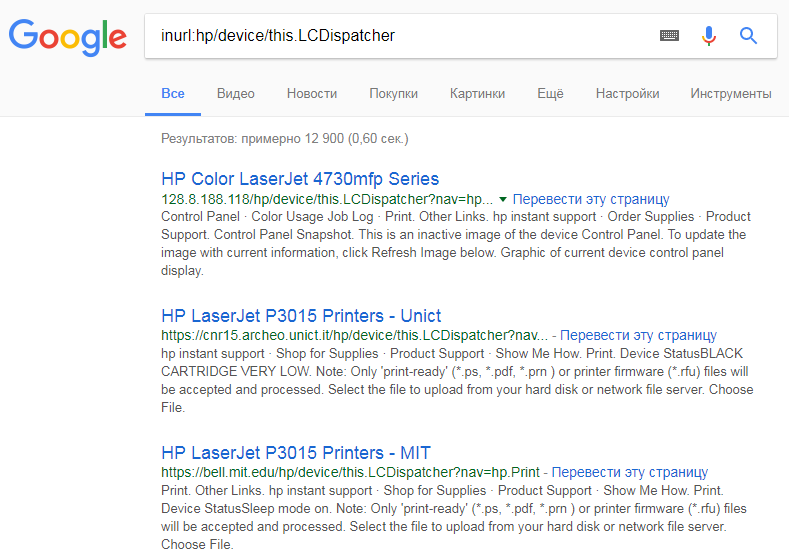
Thousands of vulnerable HP printers with an open control panel can be googled by any user
“Only our staff members knows about the service”
Myth
If a company develops a web service that will not be advertised, there is no need in Internet security.
Reality
Remember:
- Registration of domain names is tracked not only by "domain parkers", but also by hackers, since the attack on the developed service has a better chance of success;
- On the subdomain part, the address can be guessed using a trivial search or as a result of exploiting the vulnerabilities of DNS servers;
- The accidental publicity at correspondence, the mention in log-files and hundreds of other reasons lead to the the service popping up in the search engines.
How to protect company's internal services
A unique solution that would prevent information leaks, negate network attacks and provided guarantees, does not exist.
There are a lot of universal advice:
- Turn away from simple passwords;
- Timely installation of updates;
- Protecting personal devices of employees;
- Implementing DLP and IPS systems;
- Buying firewalls and antiviruses.
No safety system can exclude the human factor, and reducing its impact on the security of the organization depends on the staff. While staff do not have the motivation to follow elementary precautions, "automatic" is useless. The simplest option is to increase the awareness of employees about cyber threats in particular and information security in general. If you are developing an internal service yourself, remember that the "security for later" approach will not work. When the system is up and running, its security issues are only dealt with when a real incident has already occurred.
How to get out of a vicious circle
Establish safety requirements at the specification stage. So security is introduced as the functionality of the application, and not as a service. If the company has already launched dozens of internal services developed without regard for security requirements, then as a first step, we recommend assessing the current state of information security of internal resources, possible risks and develop a set of measures to reduce possible damage. The best solution is to ask specialists to audit the system and repeat this procedure annually.